Outlining Infrastructure for a Social Media Training Certifying Authority
A practical use for NFTs to mitigate online aggression and cyber physical attacks
Disclaimer: The information in this post reflects my thought(s) and opinion(s) on the subject being discussed at the time of posting. These thoughts and opinions are subject to change at any time. Factors that may play a part in changes may include change(s) in world view, additional research, more accurate research, open discussion, etc.
This paper is written as a response to and proposed solution for the issues raised in:
Training Online Social Network Userbases
The goal of this paper is to address the issue(s) raised in its predecessor. This paper aims to avoid shifting away from social media networking sites in an effort to phase these platforms out of use, I believe social media networking sites have become too engrained into society to be abandoned completely. While an idealized solution such as that would diminish the negative impacts of social networking sites impose on society it would also strip society of a world changing tool that revolutionized communication. Social networking sites, much like the internet itself, are tools that morph to fit the way(s) that society as a whole use them. Due to their continual adoption it’s essential for users to develop healthy relationships with these tools so that they can be used in a responsible way to meet goals and provide entertainment. I believe the most realistic solution to improve users’ experience and behavior on these platforms is to implement biannual online social network security training.
Numerous outlets of media benefit from the toxic culture built around invoking negative emotion in their customers to ensure maximum engagement and interaction with their material. Because of this content creators and media publishers have a vested interest in perpetuating the spread of misinformation, “fake news”, and inflammatory content to capitalize on opportunities to monopolize users’ attention. With that said, rather than outlawing the consumption of this content, users should be given the tools through awareness training to allow themselves to identify when actors with questionable motives are attempting to manipulate the users’ emotional state(s) with the goal of taking advantage of them. Security awareness training has been proven to improve employees' performance in identifying security threats in organizations of various sizes and may also be applicable to minimize the impacts of mass manipulation social engineering attacks.
“Effectively reducing misinformation would require restructuring the online environments that promote and support its sharing.” - Pamela Madrid
To maximize the applicability of this proposed awareness training it should be modified from being cybersecurity-centric to being social networking site content focused. Specifically, it should at minimum address predatory application design, identifying misinformation/fake information, and addictive application features1. Further topics that should be considered for inclusion in this training include methods for identifying echo chambers, the negative impacts of echo chambers, interacting with competing ideas/opinions in a positive way, and separating self worth from the attention gained from sharing misinformation.

During the World Economic Forum’s Annual Meeting of New Champions in September 2018 Jean-Pierre Bourguignon2 called on the scientific community with his statement, “We need to train a new generation of critical minds. We must tackle this issue through improved news literacy, and it is the task of our educators and society at large to teach children how to use doubt intelligently and to understand that uncertainty can be quantified and measured,” a call which Finnish educators answered. Finland, ranked 1st place in the media literacy index, has begun educating its students in both primary and secondary school on how to identify misinformation online in a way similar to what this proposed training would aim to. Saara Martikka, a teacher in Hämeenlinna, Finland, tackles these issues with her eighth grade class by providing them news articles with which they consider its purpose, how and when it was written, and what the author’s central claims are. Occasionally she will also have students edit their own videos and photo to show them first hand how easily information can be manipulated.
There are some key differences between Finland and the United States that greatly benefit Finland’s ability to address these topics in this matter. Approximately 5.4 million people speak Finnish, misinformation/disinformation articles targeted at Finnish readers will sometimes contain grammatical or syntax errors making them easier to identify, where as 1.12 billion people speak English. Finland also has one of the greatest public school systems in the world which prioritizes education equality for all students with 93% of Finns graduating high school, 17.5% higher than the United State’s percentage of high school graduates. In contrast, the United States has a disparity of education available for students across the country stemming from school segregation by income, leading to variances in the quality of education provided. Furthermore, the Finnish public have a high level of trust in the Finnish government while the United States public have been progressively losing trust in their government over the past 50 years resulting in near historic lows.
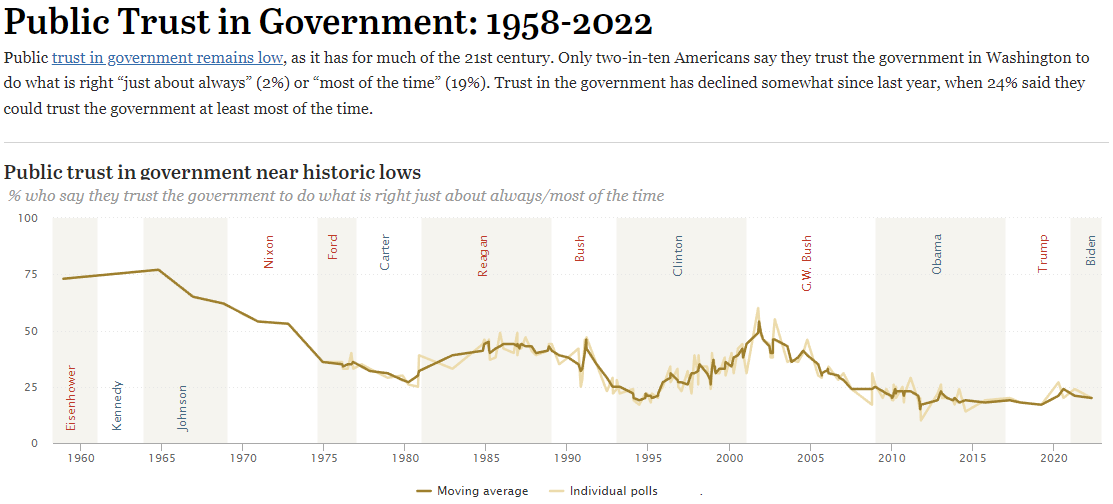
When considering all of these factors I believe the best course of action to take would be for law makers to pass legislation regulating online social networks by directing them to require categorically specific site training as part of prerequisites to site access. This would allow standardization of education countrywide in addition to ensuring 100% compliance from userbases attempting to access online social networking sites. These trainings could be created by necessary governing bodies and subject matter experts to address essential information and methods for healthy use for the categorized networking site. The trainings would be specialized for social networking sites based on categorization of the site’s media and disseminated from the organization creating them. The organization should utilize a decentralized autonomous organization (DAO) structure to address the public’s distrust or lack of trust in the United States government.
The online social network training may initially be given once every 6 months for each online social networking site being accessed by a user to attempt to improve the user’s awareness of the effects of usage along with attempting to create a more healthy relationship with social networking sites. This timetable should be updated post implementation to attempt to optimize the trainings’ impact(s), for example some organizations see improved effects with monthly training rather than annual training. To minimize overtraining, the implementation of a DAO based decentralized certifying authority can issue non-fungible tokens (NFTs) to verify that a user has taken training within the past 6 months (or the adjusted timetable) to allow the user to avoid retraining within that timeframe. These NFTs can be presented from the user they were issued to the social networking site the user is attempting to access in order to bypass training requirements for sites with which they hold NFTs of the same category.
Decentralized Certifying Authority Infrastructure
A decentralized model for training is an ideal course of action to attempt to restore public trust and secure public buy in, this can best be achieved via the creation of a DAO3. To establish the DAO for a certifying authority, a blockchain will need to be created for its smart contract to be built on top of. Utilizing a DAO structure will allow for greater overall transparency and public verification of actions from the certifying authority. The DAO should be comprised of a combination of the following government and independent stakeholders:
Nodes representing any of these organizations should be created with voting rights enabled core membership NFTs to ensure updates to the network are possible. Ideally, as many of these organizations as possible will be included in the network so that collusion during voting decisions becomes too cumbersome to be viable. Further transparency is possible by allowing public stakeholders to join the DAO by receiving a public level membership NFT. Public level membership will be a non-voting right membership to address risk(s) that bad actors would attempt to maliciously alter decision making processes but still allow users to monitor the network first hand if they so choose.
The various social network trainings can be maintained via a decentralized file storage platform. The files would be sharded, with the shards being housed on the core NFT nodes to ensure perpetual availability of all chunks of data (assuming there is no use case in which a core NFT node would drop off of the network). Providing shards to public nodes should be avoided due to the volatility of these potentially unnecessary 'oversight nodes’ in use cases other than for redundancy. Upon the completion of necessary social network training for a user a corresponding NFT can be minted and issued to that user which would be stored in their own personal crypto wallet, maintaining the current opportunity for pseudo-anonymity available on the internet.
Training NFTs would be considered a training certification needed as prerequisite for any/all online social networks a user attempts to access. As previously stated, these training certifications would be separated by category with the user being able to maintain/hold one certification per category, with the most recent training certificate of each category taking precedence.
On the user side, online social network training certificates would be minted either with a timelock feature integrated into the NFT smart contract which would deem the NFT invalid after 6 months (or the specified time interval) or an expiration feature which would force the NFT to self destruct 6 months after minting. Training certificates would also need language included in their smart contracts to either be soulbound4 after being issued or to be marked as invalid after having greater than 1 owner. Methods for implementing a property similar to soulbinding have yet to be perfected in the web3 space but potential techniques include utilizing the proof of attendance protocol (POAP), binding NFTs to a user's ENS name, and/or utilizing the proof-of-humanity protocol.
On the online social network side, the site can inspect users’ crypto wallets to verify a necessary training NFTs are present. The site can then call a function within the NFT’s smart contract to have its timestamp returned then compare that timestamp to the date and time of inspection. If the difference in time between the timestamp and inspection time is greater than 6 months the site can deny access to the user until training is taken or a valid NFT is presented. Upon denial of access the site can offer a redirect to wherever the relevant training is located in the decentralized file storage platform. The optional redirect would serve as a quality of life feature and ideally assist with access requirement transition for the userbases. User transition from previous online social network use requirements to the newly proposed requirements should be considered at all stages of development. Initial transition for userbases should be as minimally invasive as possible to avoid substantial amounts of pushback. As the paradigm for online social networks shift, trainings of higher frequency can and should be considered based on quantified results of user habit improvement.
This paper was written exclusively by a human.
For additional information, review the University of Southern California led study “Sharing of misinformation is habitual, not just lazy or biased.”
Jean-Pierre Bourguignon was previously the President of the European Research Council.
For additional information, review the Ethereum “Decentralized autonomous organizations (DAOs)” webpage.
Soulbinding is a feature in the online game World of Warcraft in which an item with this property is prevented from being traded or mailed to another character or sold in the in-game Auction House. A soulbound item cannot be transferred in any way within game.
If you found this paper interesting please consider sharing it or signing up for the Practical CyberPhilosophy newsletter.